The Critical Multi-Tenant TMS Security Assessment Framework: How to Evaluate B2B Integration Platform Vulnerabilities That 73% of Security Teams Miss Before Supply Chain Attacks Exploit Shared Infrastructure in 2026

Supply chain attacks have experienced unprecedented growth, with cyberattacks surging at nearly double the usual rate in 2025. The 2025 Verizon Data Breach Investigations Report documents that 30% of breaches now involve a third-party, a 100% increase from the 15% reported previously. For Transportation Management System (TMS) platforms built on shared infrastructure, this trend poses particular risks that most security teams overlook.
The multi-tenant architecture that drives TMS cost efficiency also creates concentrated vulnerability patterns. In multi-tenant cloud environments, multiple customers share the same physical servers and database instances. This resource sharing creates inherent security risks if isolation fails. When 75% of software supply chains have experienced cyberattacks in the last 12 months, with almost three-quarters (74%) of attacks originating from members of the software supply chain that companies were unaware of or did not monitor before the breach, the need for comprehensive vendor assessment becomes clear.
The Multi-Tenant Security Crisis Hiding in Plain Sight
The uptick in supply chain attacks began in April 2025, when cyberattacks with supply chain implications averaged 26 a month, twice the rate seen from early 2024 through March 2025. This surge coincides with increasing reliance on shared TMS infrastructure, where vendors like Oracle TM, SAP TM, and MercuryGate—alongside emerging platforms like Cargoson—face mounting pressure to demonstrate robust tenant isolation.
Multitenancy introduces significant security vulnerabilities that often remain undetected until a breach occurs. These architectural weaknesses create attack vectors across shared databases, permission structures, supply chains, platform updates, and compliance mechanisms. The problem extends beyond theoretical risks. One of the most common methods for a cross-tenant attack in cloud environments is through misconfigurations. These can happen when resources are incorrectly set up, allowing attackers to access data or services not meant for them.
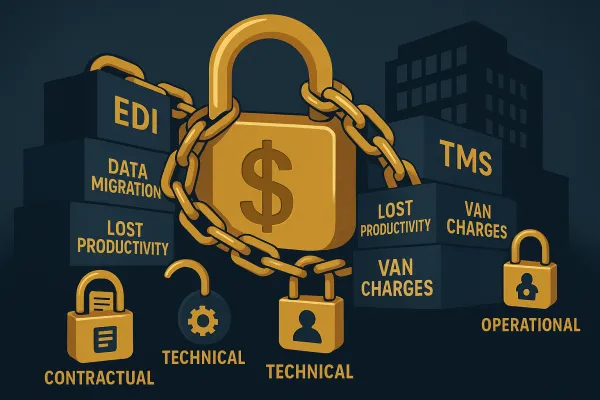
Specific vulnerability patterns include OAuth token abuse through over-permissive roles or exposed OAuth tokens that can lead to privilege escalation, tenant isolation failures where a breach in network isolation can lead to data exfiltration, lateral movement of malicious actors, or unintended access to sensitive services, and API security gaps where insecure APIs represent particularly dangerous vulnerability points. When multiple tenants access common API endpoints, a single exploited vulnerability can potentially affect all connected customers.
The Five Critical Security Domains Most TMS Evaluations Miss
Traditional TMS vendor evaluations focus on functional capabilities while overlooking fundamental security architecture. Here are the domains that determine whether your chosen platform becomes an asset or liability:
Tenant Isolation Architecture
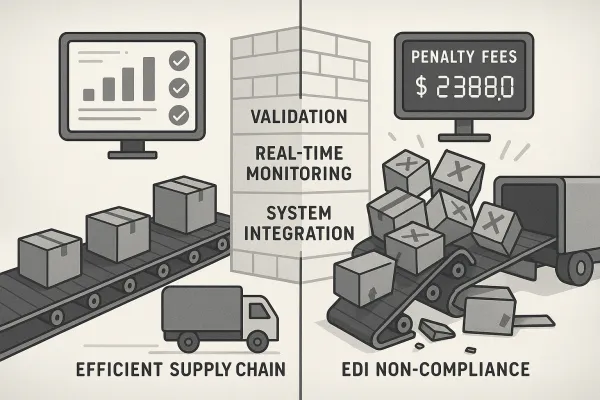
In a multi-tenant arrangement, a crucial issue emerges: How can we make sure tenants neither maliciously nor inadvertently access each other's data or resources? Effective isolation requires three layers: database segregation that goes beyond simple row-level security, network segmentation that isolates EDI systems from other infrastructure. EDI connections should terminate in a DMZ or isolated network zone, not directly into your internal network, and access control boundaries that prevent privilege escalation.
Many vendors claim "secure multi-tenancy" without providing architectural details. Ask specific questions about hypervisor separation, shared memory protections, and cross-tenant data leakage prevention. Research demonstrates that attacker-controlled Docker containers on AWS/EKS could reliably detect and co-locate with victim containers, achieving over 90% success in co-residency attacks.
Integration Security Posture
TMS platforms depend on extensive third-party integrations—ERP connectors, carrier APIs, customs systems, and EDI networks. Data transmission represents the most obvious vulnerability. Information moving between trading partners crosses multiple networks and systems, creating numerous potential interception points.
Evaluate how vendors secure these integration points. Modern platforms should implement certificate-based authentication, multi-factor authentication, and API keys with fine-grained permissions across all connector types. Legacy integration patterns using FTP or unencrypted protocols should trigger immediate red flags.
Identity and Access Management
Authentication failures in multi-tenant systems have unique consequences. One small routing mistake can send a login request to the wrong tenant's identity configuration. Nothing crashes. No alert fires. But a user from Company A is now authenticated inside Company B's tenant.
Examine OAuth implementation, SSO security, and credential management policies. Traditional identity and access management tools struggle with the granularity required for proper tenant isolation in multitenancy environments. They typically focus on application-level permissions rather than tenant-specific boundaries within applications.
Data Flow Security
Multi-tenant platforms create complex data flows that traditional security controls can't adequately monitor. Most legacy solutions treat SaaS applications as "trusted" destinations once authenticated, missing critical cross-tenant activities. While a firewall might log a connection to Microsoft 365, it cannot detect when a privileged user in IT accidentally accesses or modifies data across tenant boundaries.
Require detailed explanations of encryption at rest and in transit, logging capabilities that capture cross-tenant activity, and audit trail integrity that supports forensic investigation. Modern platforms should provide tenant-aware monitoring that traditional security tools cannot deliver.
Incident Response Readiness
Platform-wide updates in multi-tenant environments create synchronized vulnerability windows. When cloud providers deploy changes, all tenants become simultaneously exposed to any undiscovered flaws. This makes incident response planning more complex than single-tenant scenarios.
Assess vendor capabilities for breach containment, cross-tenant impact prevention, and communication protocols during incidents. EDI security isn't a project with a completion date; it's an ongoing operational requirement. Threats evolve, systems change, and new vulnerabilities emerge constantly.
The Shared Infrastructure Vulnerability Assessment Checklist
Use these technical questions to evaluate vendor claims about tenant separation and security architecture:
Database Architecture Questions: How do you prevent cross-tenant data leakage at the database level? Do you use separate database instances, schema isolation, or row-level security? What happens if a query accidentally omits tenant filtering? How do you handle database backups and disaster recovery across tenants?
Network Isolation Verification: What network segmentation exists between tenants? How do you prevent side-channel attacks through shared infrastructure? Can you demonstrate that tenant A cannot observe tenant B's network traffic patterns?
API Rate Limiting and Throttling: How do you prevent one tenant from consuming resources that impact others? What happens during denial-of-service attacks against specific tenants? How do you isolate API performance across the multi-tenant platform?
Cross-Tenant Data Leakage Prevention: What controls prevent accidental data exposure during system maintenance? How do you handle shared caches, temporary files, and log aggregation? What testing validates tenant isolation during updates?
Red flags to watch include vague answers about "industry-standard encryption," inability to explain specific isolation mechanisms, reliance on application-level controls without infrastructure separation, and lack of tenant-specific security monitoring.
Supply Chain Attack Vector Analysis for TMS Platforms
Attackers increasingly exploit trusted vendor relationships rather than attempting direct intrusion. Supply chain cyber attacks exploit the implicit trust between businesses and their vendors, leveraging a single vulnerable link to infiltrate multiple organizations.
For TMS platforms, attack scenarios include OAuth token abuse where compromised service accounts gain access to multiple tenant environments, EDI connector compromise that allows data manipulation across trading partner networks, API integration security gaps where cybercriminals can exploit vulnerabilities to gain unauthorized access to sensitive information exchanged through EDI, with attackers intercepting communications between trading partners, potentially altering information or capturing sensitive data.
Recent examples demonstrate the severity. The CrowdStrike update incident affected approximately 8.5 million Windows machines, highlighting the risks inherent in widely used tools. Similarly, the CDK Global ransomware attack disrupted U.S. and Canadian auto dealerships, resulting in losses exceeding $1 billion.
Prevention strategies require assuming compromise and building containment. Implement network segmentation that limits blast radius, monitor for unusual cross-tenant activity patterns, maintain offline backups that attackers cannot encrypt, and develop incident response plans specific to multi-tenant platform breaches.
Building Your Vendor Security Scorecard and Decision Matrix
Create a weighted scoring framework that reflects your risk tolerance and business context. Weight tenant isolation architecture at 30% for high-security environments, integration security posture at 25%, identity and access management at 20%, data flow security at 15%, and incident response readiness at 10%.
Map vendor responses to specific risk categories. Established players like Oracle TM and SAP TM typically score high on incident response readiness but may have legacy architecture limitations. Cloud-native platforms including SPS Commerce, Cleo, and Cargoson often excel at modern security controls but may lack the extensive compliance certifications required for regulated industries.
Include contract negotiation requirements such as security breach notification timelines, liability allocation for cross-tenant incidents, audit rights and penetration testing permissions, and right to audit vendor subcontractors and cloud providers.
Your ongoing monitoring framework should include quarterly security posture reviews, annual penetration testing of your tenant environment, continuous monitoring of vendor security incidents, and regular assessment of new threat vectors affecting multi-tenant platforms.
Implementation Roadmap: From Assessment to Secure Operations
Phase your security validation during vendor evaluation. Start with architectural assessment including detailed tenant isolation review, integration security analysis, and identity management evaluation. Follow with proof-of-concept testing that includes cross-tenant access attempts, performance under security controls, and incident response simulation.
Validate vendor security claims through independent testing rather than accepting compliance certificates alone. While standards like HIPAA, SOX, and PCI DSS provide guidance, they often reflect a minimum baseline; good security starts where compliance ends.
Post-implementation security monitoring requires tenant-aware security tools that traditional enterprise security cannot provide. Deploy cloud-native security tools, Security Information and Event Management (SIEM) systems, and AI-driven anomaly detection to spot odd behaviour patterns, illegal access attempts, and possible breaches before they become serious.
Establish incident response integration with your chosen vendor. Most organizations discover too late that their vendor's incident response procedures don't align with their internal requirements. Define notification timelines, escalation procedures, and communication protocols before you need them.
The 2026 Security Compliance Convergence Challenge
Regulatory requirements increasingly target multi-tenant platform security. GDPR enforcement has expanded to include vendor security posture as part of data controller obligations. PEPPOL AS4 security implications affect European trade, while cross-border data protection compliance becomes more complex in shared environments.
Cloud governance has become a market differentiator in compliance-driven markets for multi-tenant platforms. Organizations that get ahead of this trend will have competitive advantages in vendor negotiations and customer trust.
Future-proofing your security architecture decisions means choosing vendors that treat security as core product capability rather than compliance checkbox. By embracing cloud-native platforms, API-driven integrations, automation, and advanced security measures, organizations can ensure that their EDI processes are future-proof and aligned with the demands of modern commerce.
Start your security assessment now. The window between supply chain attack techniques and vendor security improvements continues to narrow. Organizations that delay comprehensive security evaluation of their TMS vendor relationships risk becoming the next headline about preventable third-party breaches.