The Critical X12 008060-TMS Vendor Consolidation Risk Matrix: How to Navigate EDI Standards Migration During the $2.1 Billion Transportation Software Acquisition Wave Without Breaking Zero Trust Security or Trading Partner Networks in 2026

X12 published its 008060 implementation guides in September 2025, replacing the long-standing 005010 versions, just as WiseTech Global's $2.1 billion acquisition of E2open and Descartes Systems Group's $115 million acquisition of 3GTMS signal the most significant TMS vendor consolidation wave in over a decade. Meanwhile, zero trust principles shift from ambition to necessity in 2026 as security budgets tighten and identity-based threats multiply. For EDI professionals managing complex supplier networks, these three simultaneous changes create unprecedented integration risks that require immediate attention.
Your X12 008060 EDI implementation timeline now intersects with TMS vendor consolidation chaos and zero trust security mandates. Miss the planning window, and you face migration failures that could disrupt your entire trading partner network.
The Perfect Storm: Three Simultaneous Risks Threatening EDI Operations in 2026
X12 has indicated that webinars and on-demand training offerings will begin in 2026, providing deeper guidance on assessing and adopting the 008060 implementation instructions. The timing couldn't be worse. While you're evaluating 008060 migration requirements, 2026 is setting up to be a big year for logistics M&A. Your TMS provider might disappear in an acquisition before you complete your X12 standards migration.
The financial impact hits immediately. LoadPilot had built an "impressive and loyal customer base" in 20 years but its technology was aging, making it "impossible for them to compete with newer technology over the last five years". InMotion Global acquired LoadPilot TMS, with the LoadPilot system shutting down March 25, 2026. When your TMS vendor becomes an acquisition target, your EDI integration investments are at risk.
Zero trust security adds another layer of complexity. Zero-trust architecture requires no user, device or workload to be trusted by default, regardless of where it sits on the network. Your EDI connections, whether they handle X12 claims (837), enrollment (834), and remittance (835) transactions or supply chain purchase orders, must now authenticate every access request.
Understanding the X12 008060 Migration Timeline and Impact
X12 published the 008060 versions available in X12's online viewer, Glass, with access through products.x12.org under Technical Report Library > Versioned Technical Reports > Implementation Guides > 008060 Version (2025). X12 also recommended that corresponding derived schema definitions supporting direct XML syntax representation be named as permitted syntax.
The migration scope affects critical healthcare transactions. X12 recommends advancing implementation guides to version 008060 including Health Care Claim Payment/Advice (835), Health Care Claim: Professional (837), and Health Care Eligibility/Benefit Inquiry (270/271). For supply chain EDI, the timing creates resource conflicts between healthcare compliance and trading partner network maintenance.
Starting in 2026, X12 will provide mechanical comparisons between 005010 and 008060 versions, high-value revision lists, and markup of transaction set listings, with webinars beginning in the first quarter of 2026. Your implementation teams face parallel projects: X12 migration, TMS vendor evaluation, and zero trust deployment.
TMS Vendor Consolidation Risk Assessment Framework
The acquisition wave reshaping transportation management systems directly threatens your EDI infrastructure stability. AscendTMS plans to "do a dozen or more" acquisitions and is bringing on a full-time employee devoted to mergers and acquisitions. WiseTech Global's $2.1 billion acquisition of E2open and Descartes Systems Group's acquisition of 3GTMS for USD 115 million signal the most significant vendor consolidation wave in TMS market history.
Evaluate your current TMS provider's acquisition vulnerability using financial stability metrics and development roadmap consistency. Look beyond current revenue figures to understand how recent acquisitions impact the vendor's cash flow, development priorities, and customer service capacity. Product roadmap uncertainties are already surfacing as TMS platforms merge, forcing customers to decide which system to standardize on, what features will be deprecated, and how long dual support will continue.
Consider the major TMS platforms and their consolidation positions. Oracle Transportation Management and SAP TM maintain enterprise market positions, while global platforms may deprioritize European-specific features during consolidation activities. Regional specialists including Cargoson alongside MercuryGate and Blue Yonder offer different risk profiles during market consolidation.
The Hidden EDI Integration Costs During Vendor Transitions
When TMS vendors merge, your EDI connections face immediate risks. Trading partner networks require recertification, data mappings need validation, and compliance gaps emerge during system transitions. A German automotive parts manufacturer discovered their €800,000 TMS implementation mistake when their new system couldn't handle their complex carrier network across 12 European countries.
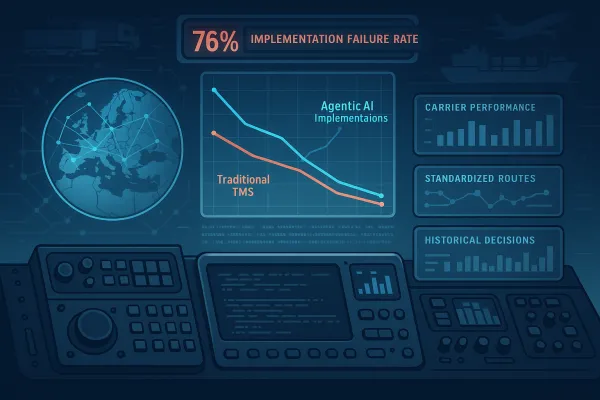
Budget for 15-25% additional EDI integration costs during vendor consolidations. Connection testing, partner recertification, and compliance validation consume resources while your team manages X12 migration projects. 66% of technology projects end in partial or total failure, while 17% of large IT projects threaten company existence, with TMS data integration facing even higher stakes.
Document your EDI connection dependencies before vendor announcements force reactive decisions. Map critical trading partners, transaction volumes, and compliance requirements across your TMS environment. Include backup connection methods and alternative integration paths in your contingency planning.
Zero Trust EDI Security Implementation During Standards Migration
Security leaders should evolve their zero trust identity roadmap from point projects into a program that is measurable, adaptive, and tightly aligned to business and compliance outcomes. Start with visibility by maintaining accurate inventory of all identities and implementing identity platforms that enforce consistent policies across cloud, on-premises, and SaaS environments with phishing-resistant MFA.
Your EDI connections require identity verification at every access point. Zero trust operates on "never trust, always verify," requiring strict identity verification for every user and device requesting access to resources, regardless of location. This includes EDI gateway access, partner connections, and internal system integrations.
Most organizations apply zero-trust principles to human users while leaving workload-to-workload communication governed by network-based trust models, but federal guidance from GSA and CISA's Zero Trust Maturity Model identify identity as a foundational pillar requiring different tools for machine-to-machine communication.
Protocol-Agnostic Security Architecture Design
Design security frameworks that survive both standards migration and vendor changes. What remains is the identity of the workload itself, and whether you can verify it at every request. Your zero trust architecture must authenticate X12 005010 connections during migration while simultaneously validating 008060 implementations.
Include identity verification across EDI protocols and TMS platforms. Zero trust requires every access request to be authenticated, authorized, and continuously validated before access is granted, with no implicit trust based on network location, device ownership, or previous authentication.
Consider security integration platform capabilities from Cleo, IBM Sterling, and other EDI providers alongside TMS security controls. Modern platforms including nShift, Transporeon, and Cargoson offer varying levels of zero trust compatibility during the transition period.
The Risk Mitigation Implementation Playbook
Create parallel testing environments that support X12 008060 evaluation, TMS vendor assessment, and zero trust validation simultaneously. Your procurement framework needs five distinct evaluation phases: vendor financial analysis, European compliance verification, carrier integration assessment, TCO modeling over 5-7 years, and implementation risk evaluation.
Build vendor diversification strategies before consolidation eliminates options. Consider core TMS functionality from your primary vendor supplemented by specialized solutions for carrier integration, compliance management, or analytics to minimize disruption if your primary vendor gets acquired.
Data portability requirements in contracts become your insurance policy against vendor lock-in, specifying formats, export procedures, and transition support that guarantee your ability to migrate operations if consolidation forces system changes. Include regular data backup requirements and audit rights to verify export capabilities.
Building Future-Proof Integration Architecture
Implement composable architecture principles that separate EDI processing, TMS functionality, and security controls. Build internal capabilities to reduce vendor dependency while improving operational resilience, developing in-house expertise for critical processes like carrier onboarding, rate management, and performance analytics.
Design API-first integration strategies that accommodate X12 evolution, vendor changes, and security updates. 39% of X12 respondents already use JSON-centric messages based on X12 transaction sets, with 78% planning to implement or expand JSON usage, meaning future "X12" will increasingly be exchanged as JSON packets with the same element structure.
Position your architecture to leverage modern integration platforms that support both legacy X12 and emerging standards. Solutions from Blue Yonder, Manhattan Active, and Oracle alongside regional specialists like Cargoson offer different approaches to composable integration during the transition period.
2026 Action Plan and Success Metrics
Execute your X12 008060 migration, TMS vendor evaluation, and zero trust implementation as interconnected projects with shared timelines and resource allocation. The procurement window for securing optimal TMS platforms before vendor consolidation eliminates choices runs through Q1 2026, giving you approximately 3-4 months of leverage.
Establish quarterly checkpoints that track X12 migration progress, vendor financial stability, and security implementation status. Include trading partner certification rates, system performance metrics, and compliance validation results in your measurement framework.
By the end of 2026, 10% of large enterprises will have mature zero trust programs, while organizations with mature implementations experience 50% fewer breaches and reduce breach costs by an average of 43%. Your success depends on treating 008060 migration, vendor consolidation response, and zero trust deployment as integrated components of supply chain infrastructure modernization.
Start vendor financial analysis immediately. Evaluate X12 008060 implementation guides through X12's Glass viewer platform while building zero trust architecture that survives the changing EDI landscape. Organizations that act decisively in Q1 2026 secure favorable positions before market consolidation and compliance deadlines eliminate flexibility.