The Zero Trust EDI Security Implementation Crisis: How to Build Bulletproof Trading Partner Networks That Survive AI-Driven Attacks and Protect Transportation Management System Integration in 2026
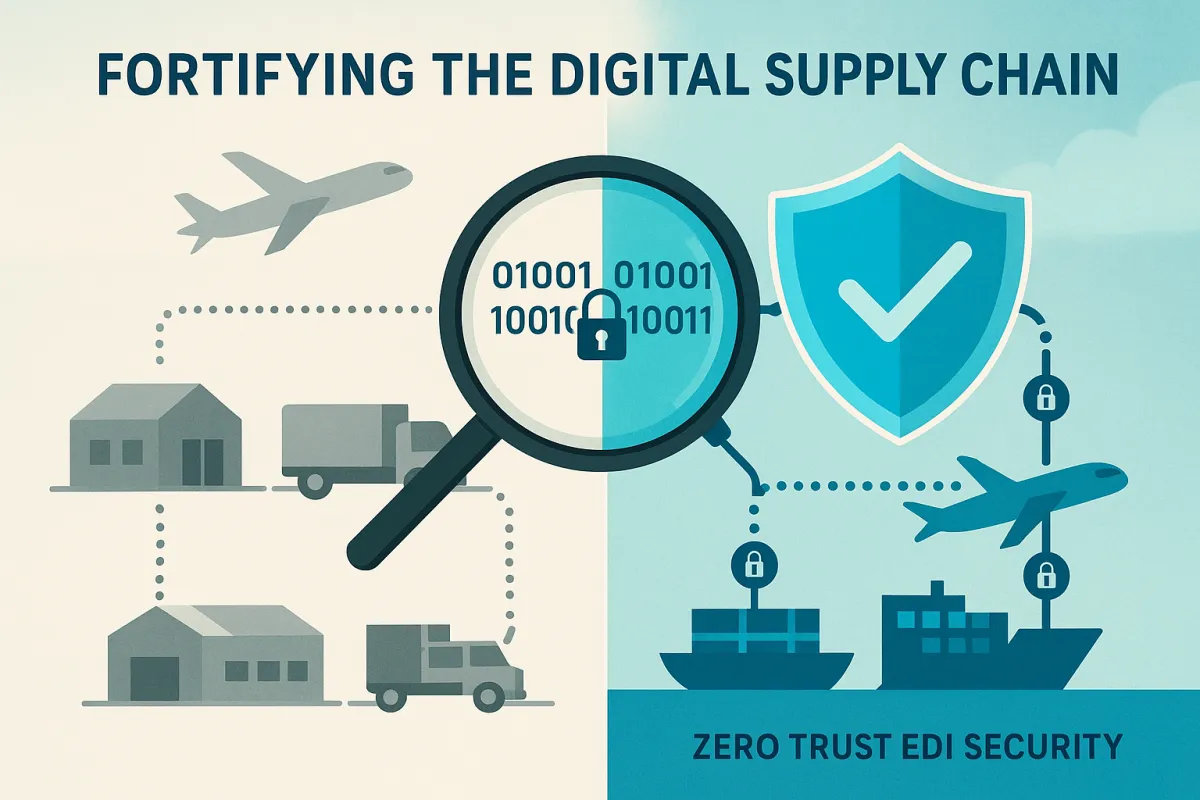
Supply chain executives are facing a cybersecurity crisis they're not equipped to handle. A 2026 survey found that while 44% of logistics companies plan to prioritize predictive visibility, only 11% cited cybersecurity as a top investment priority. This gap represents more than poor planning—it's a dangerous vulnerability in trading partner networks that process billions in EDI transactions daily.
In 2026, zero trust principles and implementation will shift from ambition to necessity. Security budgets are tightening, SOC teams aren't growing, and identity-based threats are multiplying. Yet most supply chain leaders remain focused on efficiency gains while attackers are weaponizing the very connectivity that makes modern logistics possible.
The Hidden Security Gap That's Exposing 85% of Supply Chain Networks
The numbers reveal a stark disconnect between cybersecurity investment and actual threat exposure. Logistics networks are highly attractive targets for cybercriminals. They operate complex, interconnected digital systems, including Transportation Management Systems, Warehouse Management Systems, IoT sensor networks, GPS tracking platforms, and customs portals, often integrated with dozens of third-party carriers, suppliers, and government agencies. Each integration point is a potential entry point.
Meanwhile, a study conducted by cybersecurity firm BlueVoyant shows that of the 1,500 companies surveyed, 77% of CISOs and CIOs report a complete lack of visibility into their vendors' security. At the same time, 82% have experienced at least one data breach in the past 12 months. The structured nature of EDI data creates additional vulnerabilities—IT managers face daily pressure points such as security risks and the need for supply chain visibility—yet IT managers need to make sure their organization is protected from evolving cyber threats.
Why Traditional Perimeter Security Fails in Modern TMS-EDI Environments
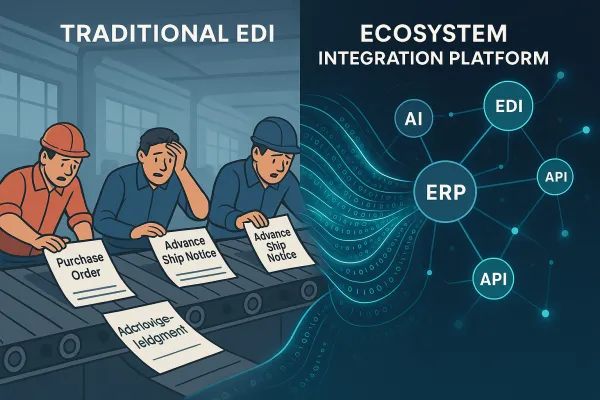
Identity has effectively become the new perimeter for modern, cloud‑heavy organizations. Traditional network boundaries have dissolved with SaaS sprawl, hybrid work, third‑party access, and automation, so attackers now focus on compromising identities rather than breaking through firewalls. The castle-and-moat approach simply doesn't work when your "castle" extends across hundreds of trading partners and cloud-based integration platforms.
Ransomware attacks encrypt critical operational systems and demand payment to restore access. A successful ransomware attack on a logistics TMS can shut down entire distribution networks within hours. Traditional perimeter defenses fail because attackers are increasingly exploiting legitimate business connections. Supply chain and third-party attacks exploit the relationships businesses necessarily maintain with partners, vendors and service providers, as well as between different applications and servers that require two-way connectivity to exchange data successfully. Once attackers compromise a vendor's systems, they can leverage that access to target dozens or hundreds of downstream organizations through legitimate business connections. Businesses often grant vendors varying levels of system access to provide services or exchange data, and each connection represents a potential entry point for hackers if that third party experiences a network breach.
The Five Critical Zero Trust Principles for EDI-TMS Integration Architecture
Zero trust EDI security requires a fundamental shift from implicit trust to continuous verification. Zero trust is a security framework and mindset that operates on the principle of "never trust, always verify," requiring strict identity verification for every user and device requesting access to resources, regardless of their location. It eliminates implicit trust by assuming all users and devices are potential threats and mandates verification at every access point through methods like least privilege access and continuous authentication.
For B2B integration environments, this means every EDI transaction, API call, and trading partner connection must be validated against security policies in real-time. Zero-Trust security assumes no transaction is safe by default, requiring continuous verification from every established trading partner. This approach mitigates supply chain risks by enforcing strict identity validation and encryption at every connection point in the network.
Principle 1: Never Trust, Always Verify Trading Partner Connections
Each trading partner connection should require explicit authentication and validation before EDI document exchange. This means implementing certificate-based authentication for AS2 connections, validating partner-specific protocols, and monitoring for deviations from established communication patterns.
When a trading partner attempts to transmit an EDI document that deviates from their usual transaction patterns—whether through timing, volume, or content structure—the system should automatically trigger additional verification steps. This approach prevents compromised partner accounts from being used to inject malicious data into your supply chain.
Principle 2: Implement Least Privilege Access for Multi-Carrier Integration
Users and devices are granted only the minimum permissions necessary to perform their specific task, reducing the potential damage from a compromised account. In TMS environments, this means each carrier integration should have access only to the specific functionality and data required for their role.
For example, a last-mile carrier should have access to final delivery data but not to upstream supplier information or financial details. When broad access is granted across integration points, a single compromised carrier account can expose sensitive data from multiple trading partners.
The TMS Vendor Security Evaluation Framework: Red Flags and Green Flags
Transportation and logistics companies are prime targets due to the valuable information they manage. When evaluating TMS vendors, security capabilities should be a primary consideration, not an afterthought. Leading solutions like Cargoson, MercuryGate, Descartes, and Blue Yonder are investing heavily in zero trust architectures, but the implementation quality varies significantly.
Look for vendors that demonstrate mature security practices beyond compliance checkboxes. An ISO 27001 certification appears as an essential criterion in the selection of an EDI provider. However, certifications alone aren't sufficient—you need evidence of continuous security monitoring and incident response capabilities.
Critical Security Questions to Ask TMS Vendors During Evaluation
Ask vendors for evidence, not promises, of their security controls. Request details about their zero trust implementation, including how they handle identity verification for API integrations and EDI connections. Inquire about their incident response procedures and ask for examples of how they've handled security events.
Pay attention to vendors who can demonstrate real-time threat detection capabilities and explain how they isolate compromised accounts to prevent lateral movement across customer environments. The best vendors will provide detailed security architecture diagrams and be transparent about their vulnerability management processes.
Step-by-Step Implementation: Building Zero Trust EDI Security in 90 Days
Start by identifying your current exposure. That means assessing configurations, visibility gaps, and policy enforcement across identity, devices, and networks. Most organizations discover that their EDI and TMS environments have significantly more exposure than they realized.
The 90-day framework focuses on practical implementation rather than theoretical frameworks. Zero Trust works best when it's grounded in execution, not theory.
Days 1-30: Security Posture Assessment and Risk Mapping
Begin with a comprehensive inventory of all EDI connections, API endpoints, and TMS integrations. Document which trading partners have access to what data and through which protocols. Map the flow of sensitive information through your B2B integration environment.
Identify implicit trust relationships that exist in your current architecture. Many organizations discover that certain legacy EDI connections operate with minimal authentication or that API keys have been shared across multiple trading partners.
Days 31-60: Multi-Layer Security Implementation
Multi-factor authentication (MFA) on all core systems, especially TMS and financial platforms, blocks credential-based attacks even when passwords are compromised. Implement MFA for all administrative access to EDI platforms and TMS systems.
Deploy real-time monitoring for EDI transaction anomalies. Set up alerts for unusual transaction volumes, unexpected document types, or communications from new IP addresses. It is up to the provider to ensure that the data flow is not subject to a "Man in the Middle" attack. It is also the provider who stores the data exchanged between EDI partners. This storage must therefore be encrypted to ensure that, even if an attacker manages to penetrate the defenses in place, he cannot exploit the data exposed to his attack.
Days 61-90: Continuous Monitoring and Validation Setup
Automate security posture assessments to detect drift early. Ongoing validation ensures your Zero Trust strategy keeps pace with reality, not just frameworks. Implement automated compliance checking for trading partner connections and establish baseline security metrics.
Create incident response playbooks specifically for EDI and TMS security events. Practice scenarios where trading partner accounts are compromised or where malicious EDI documents are detected in the system.
Future-Proofing Your Zero Trust Architecture Against Emerging AI Threats
Organizations sprint toward digital transformation, adversaries harness emerging technologies such as artificial intelligence (AI), advanced automation, and complex supply-chain ecosystems to launch attacks at unprecedented speed and scale. Attackers use AI agents to perform discovery, exploitation, and lateral movement autonomously, which drastically reduces reaction time.
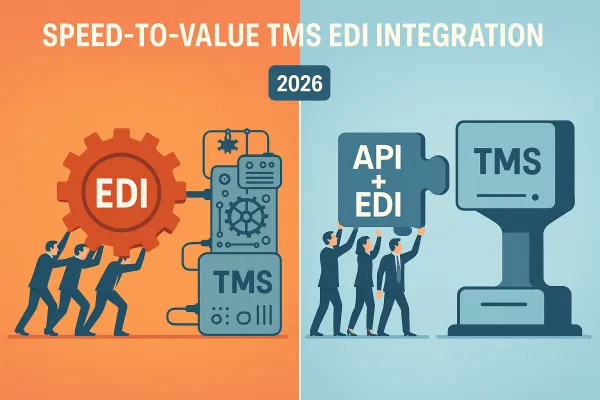
The rise of Agentic AI to automate error resolution and the move to hybrid EDI-API environments with Zero-Trust security. AI is transforming EDI by automating complex data mapping and predicting supply chain disruptions. Tools like Agentic AI can autonomously resolve transaction errors, optimizing workflows and reducing manual intervention in real-time. While these capabilities offer significant benefits, they also create new attack surfaces.
AI agents operating within EDI workflows must themselves operate under zero trust principles. This means implementing separate authentication for AI systems, monitoring their decision-making processes, and ensuring that autonomous agents can't escalate privileges or access data beyond their defined scope.
The key is building security architectures that can adapt to AI-powered threats while leveraging AI for defense. Modern TMS platforms like Cargoson, Oracle TM, and SAP TM are beginning to implement AI-ready security frameworks that can detect and respond to automated attacks at machine speed.
By 2027, supply chain security will be defined by how well organizations balance AI-driven efficiency with zero trust protection. Companies that implement these principles now will have the resilient, secure trading partner networks that tomorrow's threats demand.