The EDI Trust Paradox Crisis: How Supply Chain Attacks Are Exploiting Trading Partner Connections and Your 5-Step Zero-Trust Implementation Framework to Protect B2B Networks in 2026
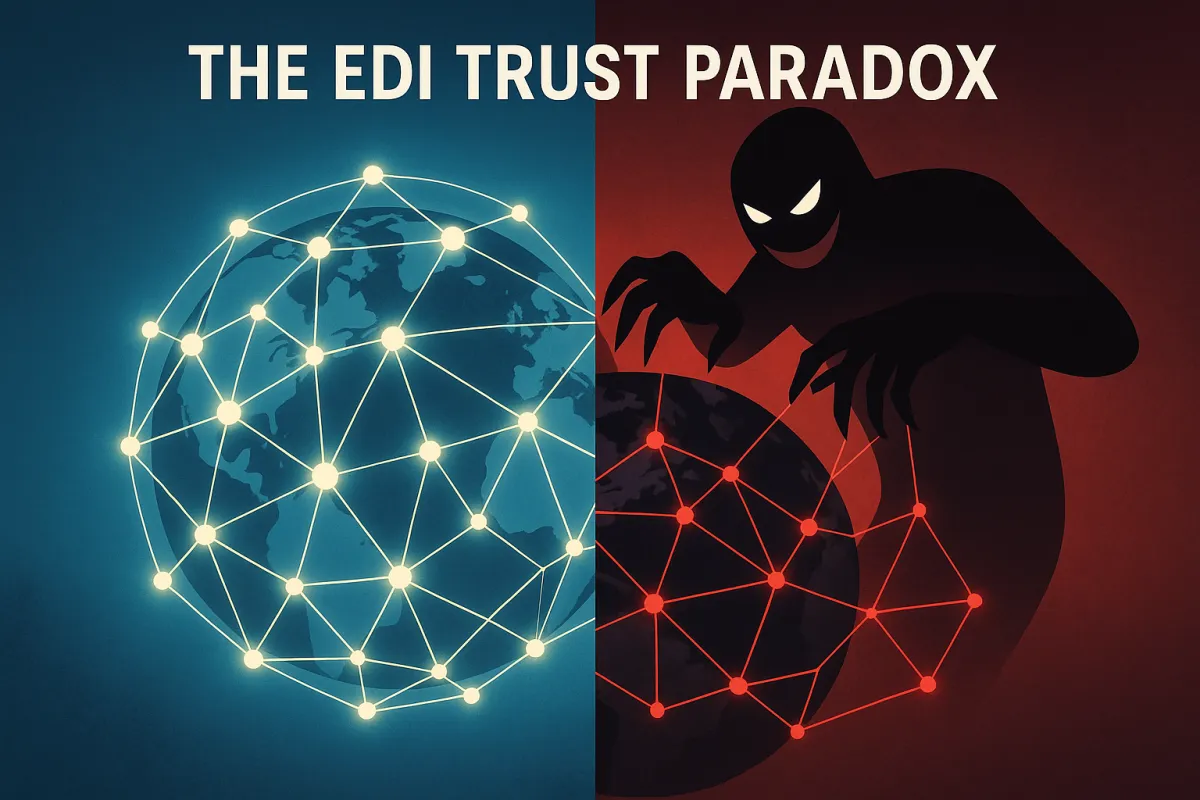
Over the past five years, major supply chain and third-party breaches increased sharply, with incidents quadrupling, according to IBM's 2026 X-Force Threat Intelligence Index. But here's the paradox that's keeping EDI directors awake at night: the very trust relationships that make EDI efficient are becoming the primary attack vector for catastrophic supply chain breaches. Cybercrime is no longer defined by single breaches. It is defined by cascading failures of trust.
European cargo theft alone costs €8.2 billion annually, but the real damage comes when attackers exploit compromised trading partner credentials to access downstream EDI networks. Once attackers compromise a vendor's systems, they can leverage that access to target dozens or hundreds of downstream organizations through legitimate business connections.
This creates what security researchers are calling the "EDI trust paradox." Your EDI system depends on authenticated connections with trading partners, but those same trusted connections become highways for attackers once a single partner falls victim to compromise.
The €8.2 Billion Problem: How Supply Chain Attacks Are Targeting EDI as the New Attack Vector
This can include note-taking applications, EDI connectors, fileshare storage servers, cloud-connected APIs and much more – while your cyber defense may be solidified against external infiltration, these types of attacks can bypass those controls via your vendor's credentials and native connections to your systems.
The numbers tell a disturbing story. IBM X-Force observed a 44% year-over-year increase in the exploitation of public-facing applications, with EDI endpoints becoming prime targets. In the past year alone, we have seen a threefold increase in software supply chain attacks, with attackers specifically targeting the trusted integrations that EDI networks depend on.
Consider the recent Trivy supply chain attack, where security scanners themselves became weapons. The attack demonstrated how legitimate tools in trusted workflows can be weaponized to compromise entire networks. For EDI systems, this pattern is particularly dangerous because whenever business partners exchange electronic documents such as purchase orders or invoices, there is always some risk that confidential information could be compromised by a third party.
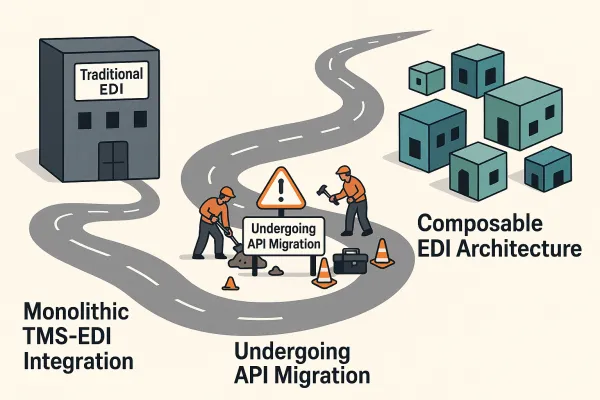
Major TMS platforms are scrambling to respond. Major TMS vendors like Oracle TM, SAP TM, and emerging European players like Cargoson have responded by developing advanced security features specifically targeting these new threat patterns. Yet traditional EDI security approaches aren't keeping pace with the sophistication of modern supply chain attacks.
The Fundamental Trust Paradox in EDI Networks
An introduction to the concept of trust and how it fits within EDI is discussed. The EDI risks categories and its influences on trust are analyzed and examined. The core issue isn't technical—it's architectural. EDI was designed around the concept of trusted trading relationships, where authentication equals access.
But "We're moving into a world of untrusted systems," said Bruce Schneier, a cybersecurity and public policy specialist at the Harvard Kennedy School. When your logistics partner's credentials are compromised, attackers inherit their trusted access to your EDI endpoints. They don't need to break through your perimeter defenses because they're already inside the trust boundary.
Lost Trading Partner Trust: EDI systems that are non-compliant or insecure can lead to rejected transactions, late deliveries, and breakdowns in partner communication. The damage extends beyond immediate security breaches to fundamental relationship breakdown between trading partners.
Why Traditional EDI Security Is Failing Against 2026 Attack Patterns
Legacy AS2 encryption and VAN security protocols were designed for a simpler threat landscape. Despite these measures, vulnerabilities persist, making it crucial to understand the limitations of EDI. In 2024, the average cost of data breaches increased by 10% to USD $4.88 million, the highest on record.
The problem isn't just technical—it's behavioral. The previous year saw a major evolution in cyber attack capabilities and trends, from AI granting even amateur hackers the ability to scale virtually endlessly to critical threats against software supply chains and integrated ERP infrastructure.
Modern attackers use AI to automate reconnaissance of EDI networks. They map trading partner relationships, identify high-value transaction flows, and position themselves for maximum impact. "I always say that attackers tend to follow the path of least resistance," while still having a high return on their efforts. North America fits both, offering scale and payoff for the attacker." European networks face similar targeting, with attackers specifically exploiting cross-border EDI complexity.
The Three Critical Security Gaps Most EDI Teams Miss
First: Identity verification becomes meaningless when trading partner accounts are compromised. Some common vulnerabilities include: a) Unauthorized Access: The sensitive nature of EDI data makes it an attractive target for cybercriminals seeking to gain unauthorized access and exploit it for their gain. Your system authenticates the attacker using legitimate credentials from a breached partner.
Second: Session monitoring gaps create blind spots. Misconfigurations, outdated software, and unsecured connections are the leading causes of EDI vulnerabilities. Understanding these risks and how to prevent them protects sensitive data, ensures compliance, and maintains uninterrupted business operations. Most EDI systems log successful authentications but don't monitor behavioral patterns that might indicate compromise.
Third: Transaction validation remains largely manual. Poor data quality can lead to issues like incorrect purchase orders or delayed order fulfillment. Without automated anomaly detection, unusual transaction patterns that indicate compromise go unnoticed until significant damage occurs.
The Zero-Trust EDI Implementation Framework: 5 Steps to Secure Trading Partner Networks
In today's threat landscape, enhancing EDI security with Zero Trust isn't optional; it's strategic. Adopting a "never trust, always verify" mindset is essential for protecting data, ensuring compliance, and sustaining strong business relationships.
The zero-trust approach for EDI requires continuous verification of every transaction, regardless of the source's previous authentication status. Modern platforms like Cargoson are building these capabilities natively, while legacy systems require retrofitting with additional security layers.
Step 1: Trading Partner Identity Verification and Continuous Authentication
Move beyond static certificate authentication to dynamic identity validation. To mitigate the risks of unauthorized access, robust authentication mechanisms are essential. Implementing strong password policies, multi-factor authentication (MFA), and encryption techniques can significantly enhance the security of your EDI system.
Implement multi-factor authentication for all EDI endpoints, not just administrative access. This means requiring additional verification factors beyond traditional AS2 certificates. Regular credential rotation becomes automated rather than annual, with behavioral pattern analysis flagging unusual access patterns even for authenticated sessions.
Their modern architecture allows for rapid security updates and integrates with European law enforcement databases. The platform emphasizes API-based security rather than traditional EDI approaches. Modern TMS platforms like Cargoson demonstrate how API-first architectures enable more sophisticated authentication controls than traditional EDI implementations.
Step 2: Real-Time Transaction Validation and Anomaly Detection
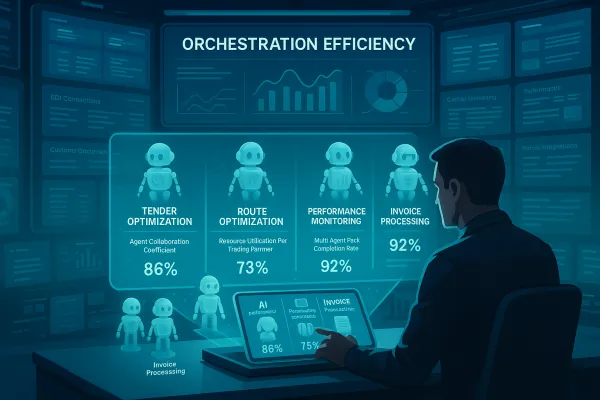
Implement AI-powered transaction monitoring that identifies patterns indicating potential compromise. Their security approach focuses on predictive threat detection, using machine learning to identify unusual patterns that might indicate security breaches. The platform's AI capabilities can predict potential security risks based on route patterns, carrier behavior, and historical data.
Monitor for volume spikes, timing anomalies, and format variations that deviate from established baselines. For example, if a trading partner suddenly begins submitting purchase orders at 3 AM instead of their normal business hours, or transaction volumes spike beyond historical patterns, automated systems should flag these for immediate review.
For example, Cargoson's platform can automatically flag shipments that deviate from normal patterns, while Oracle's system integrates with broader supply chain data for comprehensive risk assessment. The key is building detection logic that understands normal trading partner behavior and identifies deviations quickly.
TMS Vendor Security Evaluation: How to Assess Zero-Trust Capabilities Before You Sign
Vendor security evaluation requires going beyond SOC 2 compliance checklists. The key is choosing a provider with verified certifications like SOC 2 Type II and ISO 27001 that demonstrate independently audited security practices. But certifications don't reveal how vendors handle zero-trust architecture or supply chain attack scenarios.
Focus on architectural capabilities rather than feature lists. European shippers working with Cargoson or similar modern platforms access innovations immediately, while companies on legacy Oracle TM or SAP TM face lengthy upgrade cycles and additional licensing costs. Look for platforms that can implement new security features without major upgrades or additional licensing fees. Cloud-based systems typically offer faster security updates than on-premise implementations.
Evaluate how vendors handle the three major vendor categories emerging in 2026. The acquisition spree reveals three distinct market categories: global mega-vendors (Infios/MercuryGate, Descartes, SAP TM, Oracle TM, E2open/WiseTech), European specialists (Alpega, nShift, Transporeon/Trimble), and emerging European-native solutions (including Cargoson) that focus specifically on cross-border European operations.
The Critical Questions Every Security Audit Should Include
Ask vendors specific technical questions that reveal their zero-trust implementation depth. How do they handle certificate management automation? Misconfigured permissions: Without centralized access control, users may gain unnecessary privileges, which can increase exposure. Regular permission audits and tiered role assignments help keep sensitive data secure.
Behavioral analytics capabilities separate advanced platforms from basic EDI systems. Implementing robust monitoring and auditing mechanisms helps detect any suspicious activities or breaches promptly. Monitoring user access logs, network traffic, and system logs can provide valuable insights into potential security incidents. Regularly reviewing and analyzing these logs can help identify vulnerabilities and ensure timely response and mitigation.
Incident response procedures reveal vendor maturity. Proactive communication is vital for ensuring secure EDI operations. Ask how the provider discloses security incidents, scheduled maintenance, or system updates. Transparent vendors publish audit summaries and notify customers of issues in real time.
Implementation Timeline and Cost Justification: Building the Business Case for Zero-Trust EDI
The ROI calculation isn't theoretical anymore. In 2024, the average cost of data breaches increased by 10% to USD $4.88 million, the highest on record. Suffering a compromise of your data security can mean both short-term and long-term financial losses, heightened regulatory scrutiny, severe legal penalties, and lasting reputational damage.
Implementation costs vary significantly based on your current architecture. ICS2 becomes mandatory from 1 January 2026, while basic API integrations cost €5,000-€15,000, while complex ERP connections exceed €50,000. But here's the uncomfortable truth your IT director isn't telling you: budget overruns hit 75% of European TMS implementations, and 66% of technology projects end in partial or total failure.
Phased implementation reduces risk while building organizational confidence. The most successful TMS security implementations follow a phased approach that builds confidence while minimizing operational disruption: Begin with lanes carrying your highest-value cargo or routes with historical theft problems. The most successful migrations follow a phased approach: pilot with one major lane, measure results carefully, then expand systematically. This approach lets you validate security features under real conditions while limiting initial risk exposure.
The procurement window for securing zero-trust capable platforms is narrowing. European shippers who act decisively within the next 90 days—with proper frameworks that account for both capacity and consolidation scenarios—position themselves to navigate 2026's perfect storm successfully. Those who delay risk joining the statistics of failed implementations and budget overruns that plague reactive procurement strategies.
The choice isn't between security and efficiency anymore—it's between proactive zero-trust implementation and reactive breach response. "Zero Trust is foundational to becoming a business that customers, employees, and partners trust, because it blunts one of the prime causes of trust erosion — security breaches." Your trading partners expect you to protect their data with the same rigor you apply to your own operations. Zero-trust EDI implementation isn't just about preventing breaches—it's about maintaining the trust relationships that keep supply chains functioning.